AES supports 128, 192, and 256 bits key sizes and 128 bits block size. AesManaged class is a managed implementation of the AES algorithm. This article demonstrates how to use AesManaged class to apply an AES algorithm to encrypt and decrypt data in.NET and C#. AES String Encryption (CBC) Example Code for C#. GitHub Gist: instantly share code, notes, and snippets. AES String Encryption (CBC) Example Code for C#. GitHub Gist: instantly share code, notes, and snippets. Skip to content. All gists Back to GitHub. //128 bits long key Password = 'helloword'; Algorithm: PKCS5PBKDF2HMACSHA1. Encryption Key Generator. The all-in-one ultimate online toolbox that generates all kind of keys! 64-bit 128-bit 256-bit 512-bit 1024-bit 2048-bit 4096-bit.
-->Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
Operating System: Windows XP/Vista/7/8. Nexus 2 vst free. download full version.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
Asymmetric Keys
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.
See also
-->Note
No new features or functionality are being added to Media Services v2.
Check out the latest version, Media Services v3. Also, see migration guidance from v2 to v3
You can use Media Services to deliver HTTP Live Streaming (HLS) and Smooth Streaming encrypted with the AES by using 128-bit encryption keys. Media Services also provides the key delivery service that delivers encryption keys to authorized users. If you want Media Services to encrypt an asset, you associate an encryption key with the asset and also configure authorization policies for the key. When a stream is requested by a player, Media Services uses the specified key to dynamically encrypt your content by using AES encryption. To decrypt the stream, the player requests the key from the key delivery service. To determine whether the user is authorized to get the key, the service evaluates the authorization policies that you specified for the key.
Media Services supports multiple ways of authenticating users who make key requests. The content key authorization policy can have one or more authorization restrictions, either open or token restrictions. The token-restricted policy must be accompanied by a token issued by a security token service (STS). Media Services supports tokens in the simple web token (SWT) and JSON Web Token (JWT) formats. For more information, see Configure the content key's authorization policy.
To take advantage of dynamic encryption, you need to have an asset that contains a set of multi-bitrate MP4 files or multi-bitrate Smooth Streaming source files. You also need to configure the delivery policy for the asset (described later in this article). Then, based on the format specified in the streaming URL, the on-demand streaming server ensures that the stream is delivered in the protocol you selected. As a result, you need to store and pay only for the files in single storage format. Media Services builds and serves the appropriate response based on requests from a client.
Auto-Key is an automatic key and scale detection plug-in, designed to enhance your Auto-Tune workflow and save valuable time in the studio. Choosing the correct key and scale for your music is an essential part of effective pitch correction, and Auto-Key makes this quick and easy. Antares auto-tune plugin for instrument. Home of the Auto-Tune plug-in, the music industry standard for pitch correction and vocal effects. Shop and learn about the best plug-ins for pitch correction, vocal effects, voice processing, and noise reduction. Auto-Tune Pro, Auto-Tune Artist, Auto-Tune EFX+, Auto-Tune Access, Harmony Engine, Mic.

This article is useful to developers who work on applications that deliver protected media. The article shows you how to configure the key delivery service with authorization policies so that only authorized clients can receive encryption keys. It also shows how to use dynamic encryption.
For information on how to encrypt content with the Advanced Encryption Standard (AES) for delivery to Safari on macOS, see this blog post.For an overview of how to protect your media content with AES encryption, see this video.
AES-128 dynamic encryption and key delivery service workflow
Perform the following general steps when you encrypt your assets with AES by using the Media Services key delivery service and also by using dynamic encryption:
Create an asset, and upload files into the asset.
Encode the asset that contains the file to the adaptive bitrate MP4 set.
Create a content key, and associate it with the encoded asset. In Media Services, the content key contains the asset's encryption key.
Configure the content key's authorization policy. You must configure the content key authorization policy. The client must meet the policy before the content key is delivered to the client.
Reveal Sound Spire 1.1.8 VST Full Version. Reveal Sound Spire 1.1.8 VST Plugin. ANALOG / DIGITAL Superiority. Spire – the combination of best opportunities of software and hardware synthesizers. Download setup from Zippyshare 192.33 MB Download crack from Zippyshare 0.01 MB Reveal Sound Spire. The sound is simply great. Very deep, very sharp, very analog, and digital if you want it to be. On audiolove.club you can find and download a lot of fresh Spire Presets and Soundbanks for different styles of electronic music. The Spire is available as VST, AAX and AU plug-in in both 32 and 64 bit versions and works on both PC and Mac. Spire vst free download rar. Download These Free Spire Presets Since we love creating the dark, smooth and atmospheric type of sounds and samples, we decided to create these presets for Spire and give them to you for free. If you’re looking for a Spire bank with smooth, eerie, and atmospheric sounds for. Oct 04, 2018 Reveal Sound Spire (Win) VST, Plugins, Audio, Samples, Free, Download. Reveal Sound Spire (Win) October 4, 2018 Mac Synths Windows 9. 64-bit 2018 2019 analog au bass best DAW delay Download easy Editor edm eq fm free free. download full fx help high sierra hip hop izotope MAC mastering microsoft mixing mojave native instruments os x osx.
Configure the delivery policy for an asset. The delivery policy configuration includes the key acquisition URL and an initialization vector (IV). (AES-128 requires the same IV for encryption and decryption.) The configuration also includes the delivery protocol (for example, MPEG-DASH, HLS, Smooth Streaming, or all) and the type of dynamic encryption (for example, envelope or no dynamic encryption).
You can apply a different policy to each protocol on the same asset. For example, you can apply PlayReady encryption to Smooth/DASH and an AES envelope to HLS. Any protocols that aren't defined in a delivery policy are blocked from streaming. (An example is if you add a single policy that specifies only HLS as the protocol.) The exception is if you have no asset delivery policy defined at all. Then, all protocols are allowed in the clear.
Create an OnDemand locator to get a streaming URL.
The article also shows how a client application can request a key from the key delivery service.
You can find a complete .NET example at the end of the article.
The following image demonstrates the workflow previously described. Here, the token is used for authentication.
The remainder of this article provides explanations, code examples, and links to topics that show you how to achieve the tasks previously described.
Current limitations
If you add or update your asset's delivery policy, you must delete any existing locator and create a new locator.
Create an asset and upload files into the asset
To manage, encode, and stream your videos, you must first upload your content into Media Services. After it's uploaded, your content is stored securely in the cloud for further processing and streaming.
For more information, see Upload files into a Media Services account.
Encode the asset that contains the file to the adaptive bitrate MP4 set
With dynamic encryption, you create an asset that contains a set of multi-bitrate MP4 files or multi-bitrate Smooth Streaming source files. Then, based on the specified format in the manifest or fragment request, the on-demand streaming server ensures that you receive the stream in the protocol you selected. Then, you only need to store and pay for the files in single storage format. Media Services builds and serves the appropriate response based on requests from a client. For more information, see Dynamic packaging overview.
Note
When your Media Services account is created, a default streaming endpoint is added to your account in the 'Stopped' state. To start streaming your content and take advantage of dynamic packaging and dynamic encryption, the streaming endpoint from which you want to stream content must be in the 'Running' state.
Also, to use dynamic packaging and dynamic encryption, your asset must contain a set of adaptive bitrate MP4s or adaptive bitrate Smooth Streaming files.
For instructions on how to encode, see Encode an asset by using Media Encoder Standard.
Create a content key and associate it with the encoded asset

In Media Services, the content key contains the key that you want to encrypt an asset with.
For more information, see Create a content key.
Configure the content key's authorization policy
Media Services supports multiple ways of authenticating users who make key requests. You must configure the content key authorization policy. The client (player) must meet the policy before the key can be delivered to the client. The content key authorization policy can have one or more authorization restrictions, either open, token restriction, or IP restriction.
For more information, see Configure a content key authorization policy. Traktor scratch pro free download.
Configure an asset delivery policy
Configure the delivery policy for your asset. Some things that the asset delivery policy configuration includes are:
- The key acquisition URL.
- The initialization vector (IV) to use for the envelope encryption. AES-128 requires the same IV for encryption and decryption.
- The asset delivery protocol (for example, MPEG-DASH, HLS, Smooth Streaming, or all).
- The type of dynamic encryption (for example, AES envelope) or no dynamic encryption.
For more information, see Configure an asset delivery policy.
Create an OnDemand streaming locator to get a streaming URL
You need to provide your user with the streaming URL for Smooth Streaming, DASH, or HLS.
Note
If you add or update your asset's delivery policy, you must delete any existing locator and create a new locator.
Generate 128 Bit Key C Key
For instructions on how to publish an asset and build a streaming URL, see Build a streaming URL.
Get a test token
Get a test token based on the token restriction that was used for the key authorization policy.
You can use the Azure Media Services Player to test your stream.
How can your client request a key from the key delivery service?
In the previous step, you constructed the URL that points to a manifest file. Your client needs to extract the necessary information from the streaming manifest files to make a request to the key delivery service.
Manifest files
The client needs to extract the URL (that also contains content key ID [kid]) value from the manifest file. The client then tries to get the encryption key from the key delivery service. The client also needs to extract the IV value and use it to decrypt the stream. The following snippet shows the <Protection> element of the Smooth Streaming manifest:
In the case of HLS, the root manifest is broken into segment files.
For example, the root manifest is: http://test001.origin.mediaservices.windows.net/8bfe7d6f-34e3-4d1a-b289-3e48a8762490/BigBuckBunny.ism/manifest(format=m3u8-aapl). It contains a list of segment file names.
If you open one of the segment files in a text editor (for example, http://test001.origin.mediaservices.windows.net/8bfe7d6f-34e3-4d1a-b289-3e48a8762490/BigBuckBunny.ism/QualityLevels(514369)/Manifest(video,format=m3u8-aapl), it contains #EXT-X-KEY, which indicates that the file is encrypted.
Note
If you plan to play an AES-encrypted HLS in Safari, see this blog.
Request the key from the key delivery service
The following code shows how to send a request to the Media Services key delivery service by using a key delivery Uri (that was extracted from the manifest) and a token. (This article doesn't explain how to get SWTs from an STS.)
Protect your content with AES-128 by using .NET
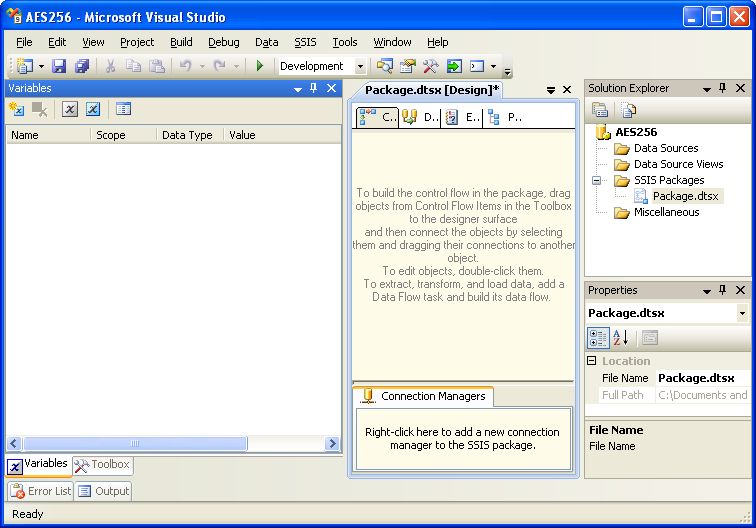
Create and configure a Visual Studio project
Set up your development environment, and populate the app.config file with connection information, as described in Media Services development with .NET. Auto-tune pro fl plugin free reddit.
Add the following elements to appSettings, as defined in your app.config file:
Example
Overwrite the code in your Program.cs file with the code shown in this section.
Note
There is a limit of 1,000,000 policies for different Media Services policies (for example, for Locator policy or ContentKeyAuthorizationPolicy). Use the same policy ID if you always use the same days/access permissions. An example is policies for locators that are intended to remain in place for a long time (non-upload policies). For more information, see the 'Limit access policies' section in Manage assets and related entities with the Media Services .NET SDK.
Make sure to update variables to point to folders where your input files are located.
Media Services learning paths
Media Services v3 (latest)
Check out the latest version of Azure Media Services!
Media Services v2 (legacy)
C# 128 Bit Int
Provide feedback
C# Generate 128 Bit Key
Use the User Voice forum to provide feedback and make suggestions on how to improve Azure Media Services. You also can go directly to one of the following categories: